What is Steganography
Steganography is an art of hiding a file, message, audio, video, or image within another file, message, audio, video, or image. The word steganography comes from two greek words "steganos" (meaning: concealed) and "graphein" (meaning: writing).
The basic difference between cryptography and Steganography is that in cryptography only the message is hidden, but in Steganography, the message and the secret communication are hidden.
A lot of good steganographic tools are available for Windows, Mac, and Linux, but not that much for the Android operating system.
Now lets see how you can do the same
GETTING STARTED
Here is how to hide any file inside any image file on android:
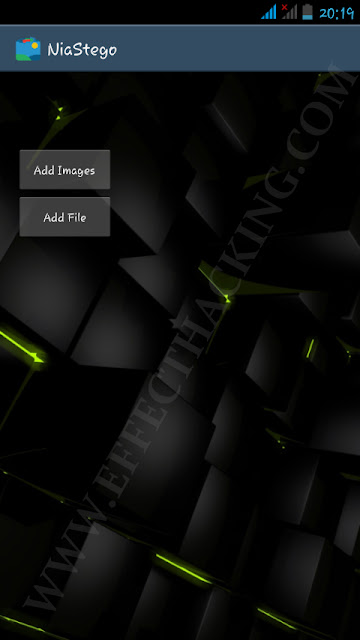
1. First, you have to download NiaStego and install it on your android device.
2. Open the app, then you will see a window as shown below.
3. Tap on "Add Images" and then select the image file(s). Then tap on "Add File" and then select the file that you want to hide inside the image(s).
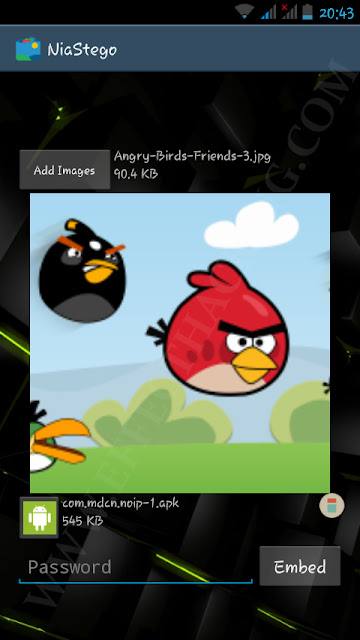
4. Enter a password and then tap on "Embed". Then wait until the process is complete.
You can find the processed image file(s) at Sdcard/NiaStego/StegoImages.
To retrieve the embedded file from an image file, select the image file and then enter the password, then tap on "Extract".
DOWNLOAD NIASTEGO
Now sit back and start hiding.

Comments
Post a Comment